Vulnerable perimeter devices: a huge attack surface

With the increase of critical gateway devices deployed to support off-premise work, companies across the world have to adapt to a new threat landscape where perimeter and remote access devices are now in the first line.
What Is Attack Surface Management (ASM)?
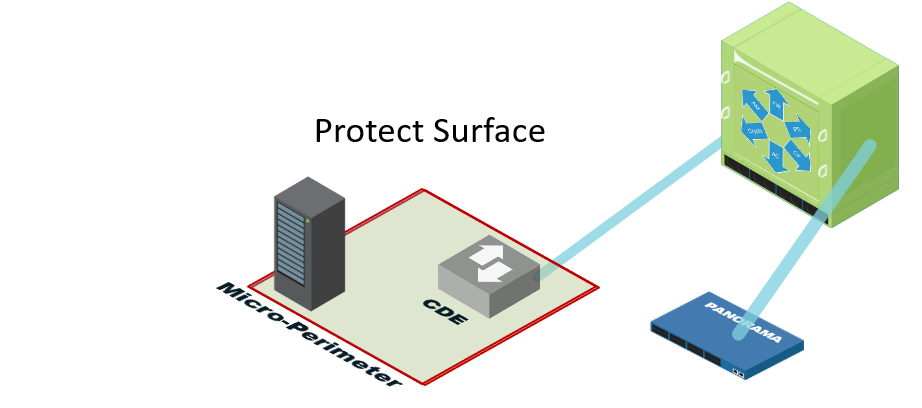
Define a Protect Surface to Massively Reduce Your Attack Surface
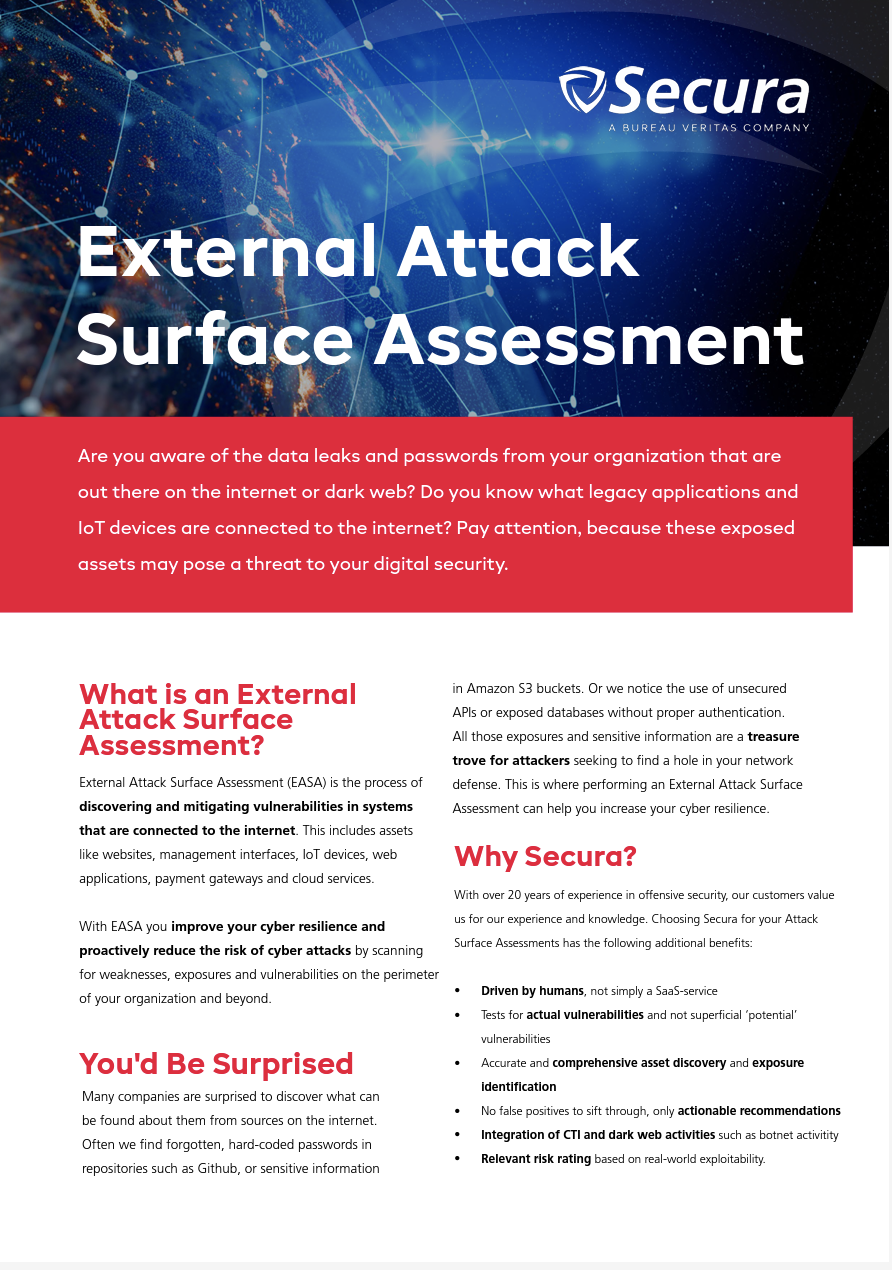
Why an External Attack Surface Assessment (EASA) is important

Four Tips for Designing a Secure Network Perimeter - SecurityWeek

Latest Remote Desktop news
Attack Surface Management External Attack Surface Analysis

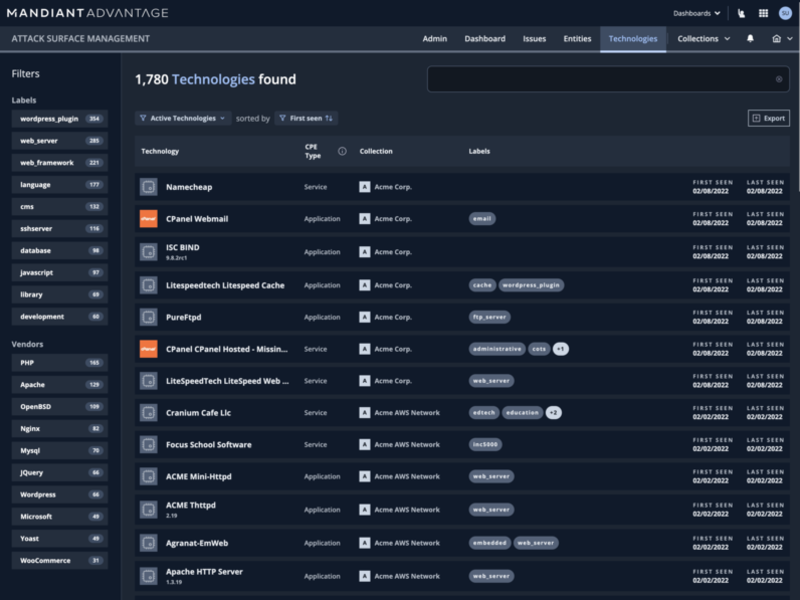
Top 8 Attack Surface Management Solutions for 2023

The Evolution of External Attack Surface Management: From Cyber
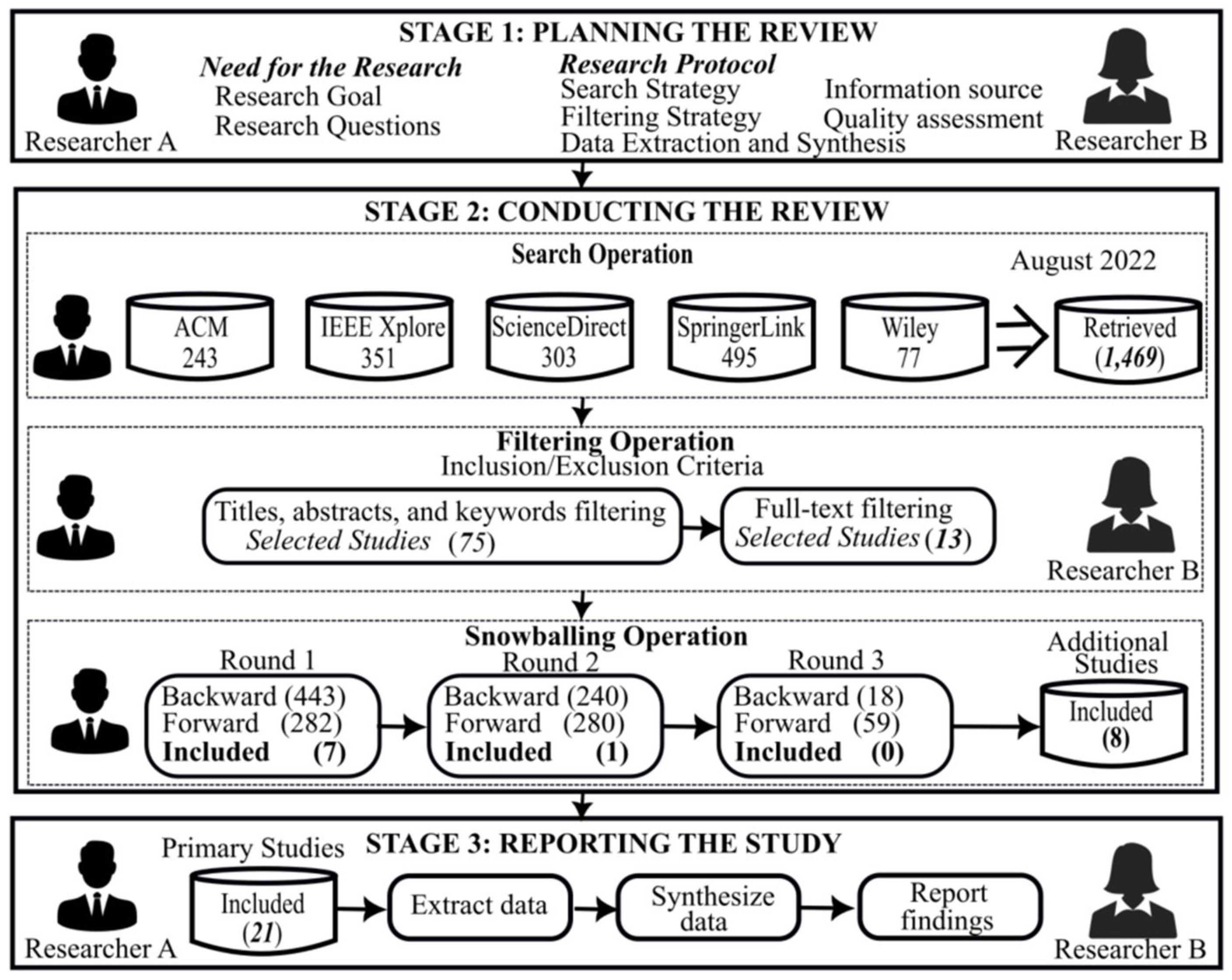
Computers, Free Full-Text

Cyber Insights 2023 Attack Surface Management - SecurityWeek

Definition And Examples Of Cybersecurity Threat Vectors

7 signs that your IT infrastructure is vulnerable to a cyber