Length extension attack. What is length extension?
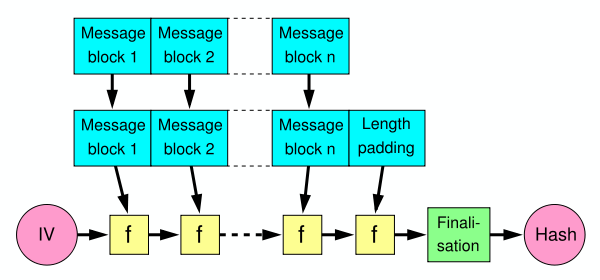
When a Merkle-Damgård based hash is misused as a message authentication code with construction H(secret ‖ message), and message and the length of secret is known, a length extension attack allows…
How did length extension attacks made it into SHA-2?

Table 1 from Why narrow-pipe cryptographic hash functions are not a match to wide-pipe cryptographic hash functions ?

Intense - Hack The Box
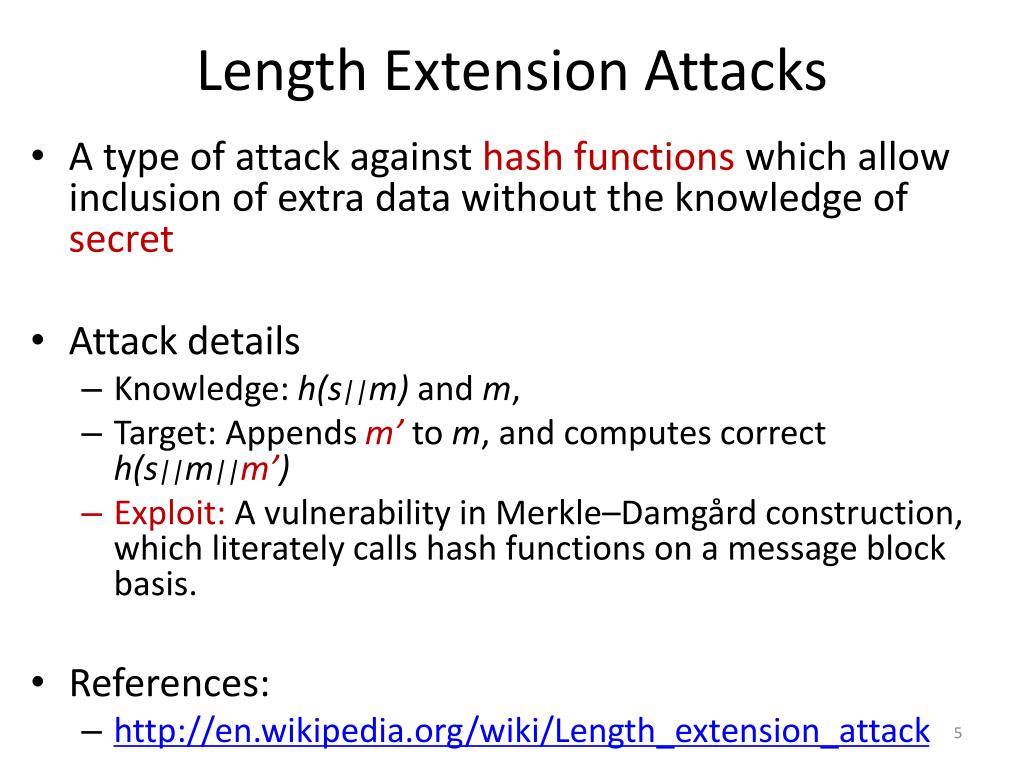
PPT - Workshop 2: Length Extension Attack PowerPoint Presentation, free download - ID:1618604

Acronym Lea Length Extension Attack Stock Illustration 487376110
Hash Length Extension Attack Lab

Dead Ends in Cryptanalysis #1: Length Extension Attacks - Dhole Moments
Length extension attack. What is length extension?, by Deep RnD
Length Extension Attack Baeldung on Computer Science

Length Extension Attack on MD4. In this article we will exploit a…, by Henrique Marcomini, Sinch Blog